We just held our fifth week of the Hacking for Defense class. This week the teams passed the half way mark in the class. They’ve collectively talked to over 550 beneficiaries (users, program managers, stakeholders, etc.) Their focus for this week was to figure out how to get products rapidly deployed into their sponsors organization. Our advanced lecture explained how to get buy-in for your solution by creating an insurgency among your supporters and advocates.
(This post is a continuation of the series. See all the H4D posts here (and also read Pete Newell’s weekly class summaries here.) Because of the embedded presentations this post is best viewed on the website.)
This is not a typical class
If you’ve been reading these weekly blogs, you’ve seen by now this is not a typical class.
The class is a combination of theory and intensive practice. First and foremost, it is experiential and hands-on. The teams live and die by the Lean Startup credo: “There are no facts inside the building so get the hell outside.” That’s why, just halfway through the class, they’ve already talked to 550 beneficiaries (users, program managers, stakeholders, etc.)
The Lean Methodology requires teams to abandon their preconceived notions of how one builds startups and solve problems – The class is designed to break students out of that all too common mindset that they understand customer’s problems, can design a solution and want to get right to work on building it – all without contact with the stakeholders, users, decision makers, etc.
After decades of teaching I have found that getting students to really change these beliefs cannot be done with reading, case studies or in-class simulations – at least not in the short time we have them in the class. If we really want them to understand how to efficiently and rapidly understand and solve customer problems, we needed to immerse them with customers on day one.
And if we want them to understand what life outside the classroom in an early stage venture will look like, then they need to experience chaos, conflicting data, uncertainty and good-enough decision making for 10 confusing weeks.
We start by pushing the teams incredibly hard to set the pace (and wash out any of those who can’t work at this pace.) Teams hit the class running. Before the first class, each team has already spoken to 10 customers, and they are challenged to present their mission model canvases within 20 minutes of walking through the classroom door. Within 5 minutes from the first time a team starts to present, they get hit with “relentlessly direct” critiques.
If you can’t see the presentation click here
But by week 5, (this week) the teams have either embraced the Lean process or we’re not going to get through to them. So at this point in the class we begin to dial down the tone and tenor of the comments, and over the next four weeks become their cheerleaders rather than their taskmasters.
In week 9 we’ll stop and use the week and class for “reflection”. We’ve found that getting the teams off the customer discovery treadmill at this point helps them to look back and reflect on what they’ve really learned, not just about their product/customers but more importantly about the lean processes, themselves, and team work.
Team Presentations: Week 5
This week the teams were primarily trying to answer how products get from demo to deployment in their sponsors agency.
In all team presentations, note that their new learnings each week are highlighted on their Mission Model canvas in red.
Sentinel initially started by trying to use low-cost sensors to monitor surface ships in a A2/AD environment. The team has found that their mission value is really to enable more efficient and informed strategic decisions by filling in intelligence gaps about surface ships from heterogeneous data.
Slides 4-27 is one of the best illustrations (actually an animation) of how all the beneficiaries work and interact. Slide 29-33 is their detailed drill-down on how their solution could get acquired and deployed in the Navy.
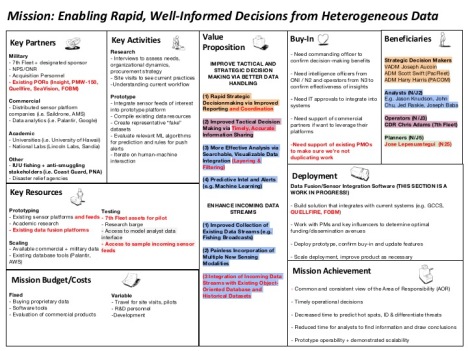
Slide 34 summarizes their current Mission Model canvas. Notice that each beneficiary has a matching value proposition. These relationships are expanded in detail on slides 35-38.
If you can’t see the presentation click here
NarrativeMind is developing tools that will optimize discovery and investigation of adversary communication trends on social media, allowing the U.S. Army Cyber Command (ARCYBER) and others to efficiently respond and mitigate threats posed by enemy messaging.
This week, in slide 3, the team further refined where ARCYBER sat in the org chart of who owned the problem within the DOD/IC and the acquisition process.
They learned about getting rapid funding of R&D and prototypes through a funding mechanism called Other Transactional Authority in slide 4. They further refined their Minimal Viable Product to product/market fit in Slides 7 and 8. Their Mission Model canvas in slide 9 has an updated set of beneficiaries now refined in the Value Proposition canvases in slides 10 – 17.
If you can’t see the presentation click here
Guardian is trying to counter asymmetric threats from commercial drones. This week the team worked to understand a day-in-the-life of a Forward Operating Base (FOB) documenting the roles of the captain, lieutenant and a private on a guard tower (slides 5 and 6). They worked on understanding how they would get a counter drone solution deployed through the Army’s Asymmetric Warfare Group (slides 7-9).
If you can’t see the presentation click here
Fishreel is combating Catfishing, the practice of impersonating an individual for malicious purposes, threatening security, privacy, and trust. Their solution will use publicly available social media data to assess whether a given userID refers to a real person, a real person acting under a false persona, or a bot. Last week we were concerned that the team was too focused on building MVPs and not enough on understanding their sponsor organization and how they buy and deploy products. The team really rose to the occasion. Slides 3-6, show their first-pass reconstruction of the sponsor organization and its procurement and acquisition process.
Slide 7-13 is an excellent discussion in figuring out the relationship of their Minimal Viable Product to product/market fit and a version 1.0 product.
Fishreel’s Mission Model canvas (slide 15) and the detailed Value Proposition canvases (slides 16-21) are case studies on how to get to true understanding of the problems of all the beneficiaries and stakeholders in an organization.
If you can’t see the presentation click here
Skynet is using drones to to provide ground troops with situational awareness – helping prevent battlefield fatalities by pinpointing friendly and enemy positions.
The team validated several critical hypotheses about technology and acquisition (slide 2), further refined their Minimum Viable Product (slide 3) and really dug into the path of getting a solution acquired and deployed in the Special Operations Command (SOCOM) in slides 4 – 9. Their summary of their learning is highlighted on their Mission Model canvas on Slide 10. Like Fishreel’s analysis, Skynet’s detailed Value Proposition canvases (slides 11 – 16) are also case studies on how to get to a deep understanding of the problems of all the beneficiaries and stakeholders in an organization.
If you can’t see the presentation click here
Capella Space is launching a constellation of synthetic aperture radar (SAR) satellites into space to provide real-time radar imaging.
Capella Space is pivoting towards commercial customers based on consistent feedback from the government. They’re finding that the government doesn’t want to pay for launch and sustainment, but instead would rather be users of commercial data.
One of the previous weeks’ hypotheses was that the Coast Guard would want and need synthetic aperture radar images and data (slide 5.) The team did extensive customer discovery at the Coast Guard 11th district command center and seemed find that the problem was not all that acute. Depressing – but great learning. They continue to believe that the National Geospatial Agency may be a potential DOD customer (slide 9), but are struggling to find the people to talk to.
If you can’t see the presentation click here
Aqualink started the class working to give Navy divers a system of wearable devices that records data critical to diver health and safety and makes the data actionable through real-time alerts and post-dive analytics. Their customer discovery helped them to understand that there were three beneficiaries (slide 2): the operators (SEAL divers), medical officers and medical researchers. Slides 4 and slide 5 show their decision process to focus on the more immediate problem – underwater geolocation. Slides 6 and 7 describe the organization of SOCOM and how products get deployed to the divers. Slide 8, their mission model canvas, highlights their new learnings about deployment and beneficiaries in red. Slides 15-17 diagrams their understanding of the product acquisition and deployment process.
If you can’t see the presentation click here
Right of Boom is trying to help foreign military explosive ordnance disposal (EOD) teams better accomplish their mission. Now they are developing systems, workflows, and incentives for allied foreign militaries with the goal of improved intelligence fidelity.
This week their customer discovery got them to the current lead in Iraq for the Joint iED Defeat Agency (JIDA) (slide 2). This helped them refine their map of how IED information flows (slide 6). They mapped how to get a product deployed in JIDA in slide 9. This is leading them to a Minimal Viable Product neither they nor JIDA expected in slide 15.
If you can’t see the presentation click here
Advanced Presentation Supporters and Advocates- Creating an Insurgency
The advanced lecture for this week explained how to create “buy-in” among all the beneficiaries. Pete Newell described how to use anecdotes, artifacts and story-telling to create an insurgency among the advocates for your solution.
If you can’t see the presentation click here
Team Learning Updates
A few of the teams independently starting writing weekly one-page status reports to their sponsors and mentors. This was a great idea. It keeps the sponsors and mentors informed and makes them feel they’re part of the team.
Hacking for Defense Goes National
This week three Universities announced their intention to offer Hacking For Defense this fall – The University of California at San Diego (UCSD), the University of Pittsburg, and the University of Rochester/ Rochester Institute for Technology.
As we scale the program, the DOD/IC sponsors have requested they have a single point of contact for the soliciting and validating the problems. So we’ll have a single site acting as the “sponsor challenge clearinghouse” for the schools that will be teaching the course.
We’ll have more to say about scaling the program, funding and the Hacking for Defense educators course in later blog posts.
Lessons Learned
- The teams are learning what it takes to turn a demo into a deployable solution that gets to the field
- The teams and sponsors are both learning how to accurately define the problem(s)
- This learning will save time, money and lives
Share this:
Filed under: Hacking For Defense, Teaching